Key Takeaways
- Zero Trust applies continuous authentication and authorization, eliminating implicit trust in networks.
- Critical elements include verifying identity, securing devices, and segmenting networks to limit threats.
- Challenges include integration with older infrastructure and the need to balance security with usability.
- AI and machine learning are taking Zero Trust to new levels by automating threat detection and response.
With advanced cyber threats evolving rapidly, established security models are often unable to provide the safety modern enterprises require. As organizations seek robust ways to protect critical data, Zero Trust Architecture (ZTA) has become an increasingly important framework. Unlike traditional security practices, Zero Trust treats every user and device as a potential threat, requiring continuous validation of their legitimacy. Solutions such as Versa next generation firewalls are often leveraged as part of this approach, providing powerful tools for enforcing granular security controls while supporting agile business operations. This paradigm shift is reshaping enterprise cybersecurity for companies of all sizes, industries, and infrastructures.
Zero Trust fundamentally challenges the assumption that anything inside the corporate perimeter should be trusted by default. Instead, the focus is on strict identity verification, device health assessment, and segmentation, even for internal interactions. While this imposes additional checks, it dramatically reduces an attacker’s ability to move laterally within a network if they gain a foothold. The approach aligns well with hybrid and cloud environments, which redefine where and how businesses operate. Modern digital initiatives, increased remote work, and the proliferation of endpoints have all intensified the demand for more adaptive security measures. As the regulatory landscape tightens and threat actors become more sophisticated, the principle of “never trust, always verify” is gaining momentum. Organizations looking to future-proof their cybersecurity must now integrate Zero Trust as a core component of their overall defense strategy. Adopting Zero Trust does present implementation challenges, especially around balancing strong security with user experience and compatibility with legacy systems. Nevertheless, the shift to this security model is underway across industries, spurred by both best practices and evolving compliance requirements.
Understanding Zero Trust Architecture
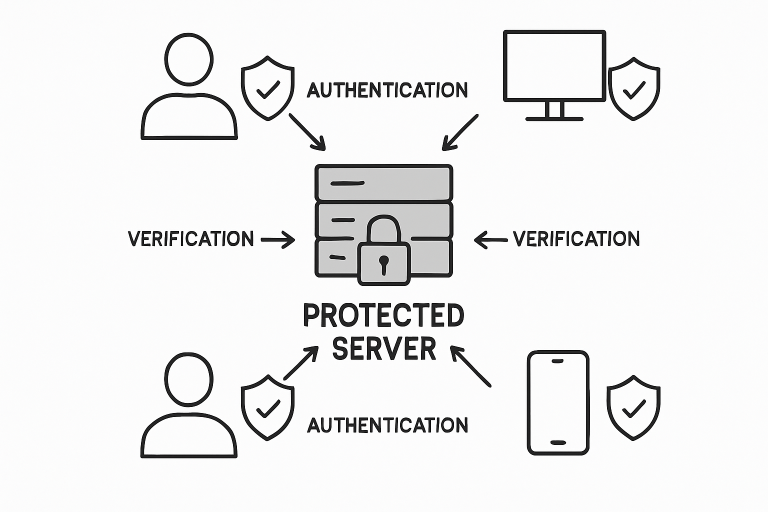
Zero Trust is not a single product but a comprehensive approach that requires all users, devices, and applications to be authenticated, authorized, and continuously validated before gaining or maintaining access. There is no distinction between users within the organization and those accessing resources from outside; all environment components are treated as if they were on an untrusted network. This blanket skepticism is essential given the rise of phishing and credential theft attacks targeting both endpoints and users at all levels of an organization.
With Zero Trust, protective barriers are placed around individual assets, applications, and data rather than just at the network edge. This minimizes the risk of breach propagation and provides more finely tuned access controls, making it significantly harder for adversaries to escalate privileges or exfiltrate information once inside.
Core Components of Zero Trust
Modern Zero Trust implementations rely on several interconnected elements:
- Identity Verification: Ensuring that every user’s identity is confirmed using techniques such as single sign-on (SSO) and multi-factor authentication (MFA). Continuous authentication checks further reduce the risk of unauthorized access, even if credentials are compromised.
- Device Security: Enforcing checks on all devices, including computers, mobile phones, and IoT sensors, to ensure compliance with security policies before granting access.
- Network Segmentation: Breaking up the network into tightly controlled segments restricts lateral movement, so even a successful compromise is contained and less damaging.
- Continuous Monitoring: Leveraging real-time analytics and monitoring solutions enables organizations to spot anomalies, detect threats early, and respond rapidly to incidents.
Challenges in Adopting Zero Trust
While Zero Trust offers superior protection, implementing this framework is not without its difficulties:
- Integration with Legacy Systems: Many enterprises operate legacy systems that were not designed with Zero Trust in mind, complicating integration and modernization efforts.
- User Experience: Additional security checkpoints can impact workflow and frustrate users if not thoughtfully deployed, requiring organizations to find a balance between safety and efficiency.
- Resource Allocation: Zero Trust transitions call for significant technology investments and strategic employee training, often demanding a phased approach to avoid disruption.
Emerging Technologies Enhancing Zero Trust
Advanced technologies are rapidly enhancing the ability of enterprises to adopt and benefit from Zero Trust:
- Artificial Intelligence and Machine Learning: AI-driven engines can detect behavioral anomalies across networks and automate responses, reducing the time needed to respond to potential threats.
- Quantum Computing: As researchers prepare for more powerful, quantum-era attacks, future-ready Zero Trust architectures are evolving. For a technical dive, examine recent work such as Quantum-driven Zero Trust Framework with Dynamic Anomaly Detection in 7G Technology: A Neural Network Approach.
Real-World Implementations
Global businesses and government agencies are demonstrating the real-world impact of Zero Trust:
- Forescout and Netskope Partnership: These companies collaborate to deliver Zero Trust solutions that unify device intelligence and cloud security for robust, adaptive protection.
- U.S. Cyber Command’s Zero Trust Lab: The military’s Zero Trust testing environments enable agencies and critical infrastructure operators to evaluate new tools before widespread adoption safely.
Best Practices for Implementing Zero Trust
- Conduct Comprehensive Assessments: Start by taking inventory of current assets, risk postures, and processes to identify high-priority improvements.
- Develop a Phased Implementation Plan: Breaking the transition into stages allows organizations to minimize business disruption and carefully scale controls.
- Invest in Training: Regular security awareness training and specialized Zero Trust workshops can increase buy-in and adoption at every business layer.
- Leverage Automation: Implement automation technologies to support continuous monitoring, threat detection, and rapid incident response.
Conclusion
Transitioning to Zero Trust Architecture is not simply a technology change but a comprehensive strategy to safeguard organizations against current and emerging threats. It helps strengthen the security perimeter at every level, protects users and endpoints, and ensures ongoing resilience against evolving cyber risks. By adopting Zero Trust principles and leveraging advanced technologies, enterprises can securely enable digital innovation while protecting vital information and infrastructure.